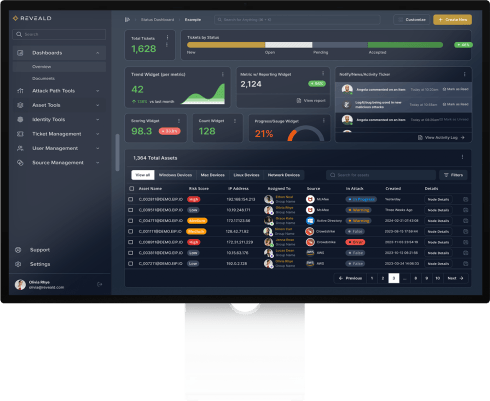
Context is King.
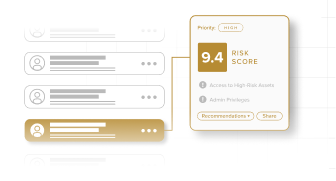
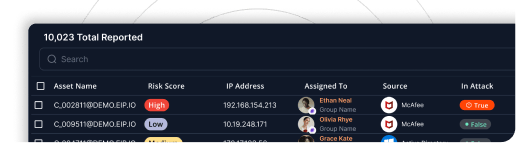
Master the attacker’s perspective – reduce business risk.
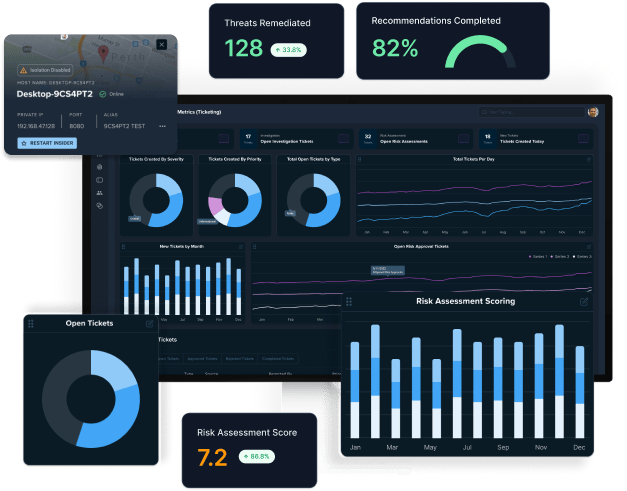
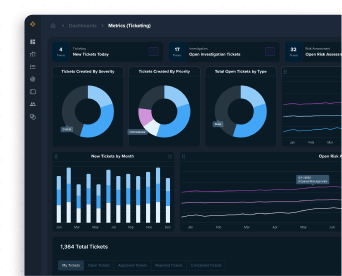
Reveald leads the next-generation in vulnerability detection and response (VDR) and Managed Detection and Response (MDR), transitioning organizations from reactive to proactive strategies with our AI-powered Epiphany Intelligence Platform.